You review financials, optimize operations, and track every lead, but what about business cyber risk? That feels abstract to most business decision makers, until it isn't. Many business owners only discover their security gaps when an invoice lands. By then, the damage is done, and the price tag carries a zero you never planned for.
This article walks you through the overlooked vulnerabilities hiding in plain sight, the hidden costs of common gaps, and how proactive planning keeps you out of crisis mode. Read it before your next cybersecurity bill surprises you.

The Cyber Risk Blind Spots That Drain Business Value
Most business leaders believe their security is good enough, but that rarely survives contact with a determined adversary. These cybersecurity risk for small business are where value quietly leaks out of your company:
- "It won't happen to us" thinking: 86% of small businesses say security is their top threat, yet fewer than 1 in 5 conduct regular risk assessments. Confidence without verification isn't strategy but wishful thinking.
- Third-party vendors as back doors: Third-party involvement in breaches has doubled, rising from 15% to nearly 30%. Therefore, your vendor's security gap becomes your breach. You don't get to opt out from the security mistakes made by your partners.
- Unmanaged devices and shadow IT: Unmanaged devices, shadow IT infrastructure, and third-party partnerships are nearly invisible to traditional security controls. However, they harbour real risk of successful exploits.
- Assuming insurance covers everything: Many SMEs hit with a cyber attack received a substantial fine afterward. Insurance helps, but it doesn't erase regulatory penalties, customer churn, or reputational damage.
- Overlooking the human factor: The majority of successful attacks are caused by human error. Your team isn't the problem, but the lack of training and the right safeguards is.
Hidden Cyber Risks Lurking in Everyday Operations
The threats that grab headlines are easy to worry about, such as massive data breaches and global ransomware attacks. However, the risks that actually catch business owners off guard are much quieter.
They live inside the routine tools, habits, and connections that keep your company running. You don't notice them because they feel normal. Until suddenly, they don't. Here are five everyday operations where hidden cyber risks quietly take root.
The Smart Devices You Forgot You Installed
Here are examples of devices you might have forgotten about:
- That internet-connected temperature logger in the warehouse.
- The smart conference room display.
- The security camera system installed three years ago by an electrician who never came back.
These devices get power and an IP address, then vanish from your mental inventory. Attackers scan for exactly this kind of forgotten hardware. Without regular oversight, a smart device becomes a smart back door.
The Remote Worker's Unsecured Home Network
Imagine that your employee works from a cozy home office, but their router is the one the internet provider gave them five years ago. The family tablet, the smart TV, and the guest Wi-Fi all share the same connection as the laptop holding your quarterly forecasts.
When personal devices get compromised, your corporate credentials travel right alongside. A home network isn't a fortress, but a shared hallway.
The Vendor You Never Audited
You hired a small marketing agency to run your social media. They have access to your analytics, your customer data, maybe even your ad accounts. However, you never asked about their password policies, and you never checked if they use multi-factor authentication.
That agency gets breached next month. Suddenly, your data is part of someone else's incident response plan. Therefore, vendor risk isn't about trust, but it’s about verification.
The Credentials Floating on the Dark Web
Every day, your employees log into email, your CRM, and your banking portal. Also, someone somewhere tries to guess their passwords using credentials leaked from a completely different service.
If anyone reused that password, the attacker now has a key to your business. Credentials don't expire just because you forgot about them. They circulate in markets you never see.
The Backup You Assumed Was Safe
You set up automatic backups years ago, but automatic doesn't mean immune. Ransomware gangs have learned to hunt for backup files first. If your backups live on the same network as your main systems, an attacker can encrypt both simultaneously.
And if you've never actually restored a backup from scratch, you don't know if it works. A backup you can't trust is just wishful thinking with a schedule. You need a more reliable system for cyber threat prevention.
The High Cost of Overlooking Common Business Security Gaps
Ignoring security gaps doesn't just leave you vulnerable, it quietly erodes value across your business. That is everything from phishing and cyber risk to ransomware risk for small businesses. Here is a table summarizing the hidden costs you’ll want to avoid:
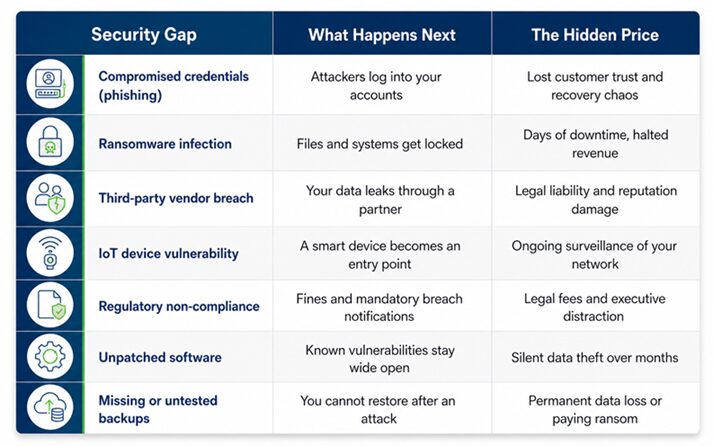
This table will help you with proactive cybersecurity planning and business data protection. Being aware of the dangers allows you to avoid operational security risks before it becomes a problem.
How an IT Service Provider Helps You Close the Gaps Before They Become Incidents
A proactive managed IT service provider stops things from breaking in the first place. Here's how that works in practice to stop risk exposure for businesses:
- Continuous risk monitoring instead of annual check-ins: Attackers work 24/7 and your defenses should too. A strategic technology partner monitors your environment in real time, detecting anomalies before they become incidents.
- Vendor risk management that extends beyond your firewall: Your security is only as strong as your weakest vendor connection. A provider assesses third-party risks, monitors vendor security postures, and ensures your entire ecosystem is secure.
- Employee training and simulated phishing campaigns: Most IT breaches start with a click. Regular security awareness training combined with realistic phishing simulations transforms your team from your biggest vulnerability into your first line of defense.
- Automated patch management and device oversight: Unpatched software is an open invitation. A provider ensures every device receives security updates automatically, closing entry points attackers actively scan for. That includes everything from office workstations to remote laptops to forgotten IoT sensors.
- Backup verification and disaster recovery testing: Having backups isn't enough to overcome business cybersecurity vulnerabilities. You need verified, tested, and regularly audited recovery capabilities. A provider ensures you can restore operations in hours, not weeks, and that your backups remain safe from ransomware targeting.

Protecting Your Business Before the Bill Arrives
The businesses that survive cyber attacks without catastrophic damage aren't the ones with unlimited budgets. They're the ones who stopped treating cyber risk as an IT problem and started treating it as a business risk. One that deserves the same strategic attention as cash flow, operations, and growth.
You don't need to become a security expert. You need a partner who is.
SafePoint IT doesn't sell firewalls and walk away. We become your strategic technology partner, embedding proactive security into every layer of your operations. That’s from your cloud infrastructure to your remote workforce to your vendor relationships.
Stop discovering your gaps the hard way. Contact SafePoint IT for a cyber risk assessment today and close the vulnerabilities draining value from your business.


