Data isn’t just a line item on your balance sheet, but the foundation of donor confidence. For nonprofit leaders, a single security lapse can unravel years of relationship-building and jeopardize funding streams. Yet, many organizations still treat IT as a reactive expense rather than a strategic asset.
We’ll share how the right nonprofit IT services will keep your organization running smoothly for years. Whether you oversee operations, revenue, or technology, understanding this shift is essential to protecting your mission and sustaining growth in an era of escalating cyber threats.

The Security Reasons Why IT Support for Nonprofit Organizations is Required
The era of assuming "we are too small to be a target" is over. That’s because cybercriminals have realized nonprofits often hold the keys to valuable assets. It includes sensitive financial data and vast networks of high-net-worth individuals.
Here is why specialized IT services for nonprofits are no longer optional:
- The lack of a physical perimeter: Your staff no longer works exclusively behind an office firewall. They log in from coffee shops, home offices, and field sites. Attackers exploit these remote endpoints, targeting the user rather than the building. Hence, nonprofit IT support focuses on securing the identity, not just the building.
- Identity as the attack vector: More cyber incidents begin with stolen credentials than technical hacks. Attackers aren’t breaking in, but they are logging in using phished or reused passwords. Without modern verification, a compromised staff email can lead directly to a drained bank account.
- Donor data is a high-value commodity: On the dark web, donor lists containing credit card details, addresses, and giving capacities are currency. A breach doesn’t just freeze operations, but it erodes the personal trust that took years to build with your major donors.
- Sophisticated AI-driven scams: Generative AI has enabled deepfake audio and hyper-personalized phishing. Imagine a finance officer receiving a call that sounds exactly like the CEO, demanding an urgent wire transfer for a "disaster relief fund." Unfortunately, traditional training struggles to spot these fakes.
- Lean teams & high turnover: Nonprofits often rely on volunteers or high-turnover staff who share passwords for convenience. An unrevoked volunteer account from two years ago becomes a silent entry point for criminals. Nonprofit IT services automate account offboarding to close these gaps.
Navigating Compliance and Governance with IT Support for Nonprofits
Compliance is often viewed as a bureaucratic headache, but in the nonprofit sector, it is the source of trust. For organizations accepting donations globally or processing grants, the regulatory web is tightening. Here is how to manage it without losing your focus on the mission.
Aligning with PCI DSS for Online Donations
If you accept credit cards, the Payment Card Industry Data Security Standard (PCI DSS) applies to you. The rules are the same if you are a $50,000 local food pantry or a $50 million international aid organization.
Most nonprofits fall into Merchant Level 4 (processing fewer than 1 million transactions annually), which typically requires a Self-Assessment Questionnaire (SAQ). However, the real risk lies in how you process donations. If your website handles card data directly, you fall under the stricter SAQ D, which has over 300 requirements.
A proactive partner ensures you are not storing card data in your donor database, which is a common and dangerous shortcut. They implement tokenization, replacing sensitive card numbers with unique tokens that are useless to hackers. This ensures that your mission is never derailed by a preventable compliance lapse.
Adhering to Global Privacy Regulations
If your donor base extends beyond your home country, you are likely subject to regulations like the GDPR in Europe or similar privacy laws in other jurisdictions. These laws dictate how you collect, store, and process donor information.
IT support for nonprofits ensures that your CRM (Customer Relationship Management) and email marketing tools have the proper data residency and consent management features. Also, you must be able to prove that donors opted in and that their data isn’t being sold or exposed without authorization.
Creating a Vendor Risk Management Framework for Third-Party Tools
Modern nonprofits run on a stack of cloud tools, which includes fundraising platforms, email marketing, cloud storage, and accounting software. The harsh reality is that you are only as secure as your weakest vendor. In 2026, third-party compromise is one of the fastest-growing attack vectors in the sector.
Therefore, nonprofit IT services must extend beyond your own servers. This involves vetting vendors before signing contracts. You should have answers to the following questions:
- Are they PCI compliant?
- Do they offer multi-factor authentication?
- Will they sign a Data Processing Agreement (DPA) that holds them liable in the event of a breach?
Without a structured vendor risk management framework, you are granting unknown entities backdoor access to your donor data.

How Strategic IT Consulting Aligns Security with Fundraising Goals
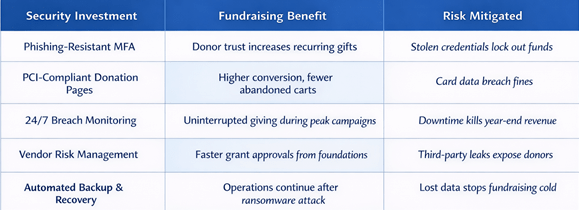
Here are just a few ways in which nonprofit IT services improve fundraising goals:
Key Components of Proactive Nonprofit IT Services
Proactive IT is about anticipating the break before it happens. For the nonprofit sector, this approach requires a unique combination of cost-awareness and technical sophistication.
Identity-First Security and Phishing-Resistant MFA
The days of SMS codes are over. Nonprofit IT support is moving toward phishing-resistant MFA, such as hardware keys or authenticator apps. This ensures that even if a staff member is tricked into handing over their password, the attacker cannot get in because they lack the physical device.
Given the high turnover in volunteer roles, automated provisioning ensures that access starts and ends precisely when it should.
24/7 Managed Detection and Response
Cyberattacks don’t keep business hours since they happen at 3:00 AM on a holiday weekend. Proactive IT services for nonprofits include a 24/7 security operations center that monitors your environment.
Furthermore, they don’t just look for viruses, but they look for behavior. If a staff member’s account suddenly starts downloading thousands of donor records at 2:00 AM, the system locks it down and alerts a human analyst before the data leaves your network.
Strategic Cloud Infrastructure Management
Nonprofits are migrating to the cloud for flexibility, but that’s not a security blanket. Proactive management involves configuring your Microsoft 365 or Google Workspace environment with strict security defaults.
This includes disabling legacy authentication protocols and enforcing conditional access policies. For example, if a staff member tries to log in from a country you don’t operate in, the system automatically blocks the attempt.
Automated Backup and Disaster Recovery
Ransomware attacks don’t just steal data, but they lock it. The difference between a devastating attack and a minor inconvenience is the speed of recovery. Proactive nonprofit IT services ensure immutable backups. That’s copies of your data that cannot be altered or deleted by a hacker.
If systems are compromised, the IT team can wipe the affected machines and restore operations from clean backups within hours instead of weeks. This ensures fundraising campaigns and program delivery stay on track.
Grant and Contract Management Integration
For nonprofits reliant on restricted funds, technology must track how money is spent against specific grant obligations. Fortunately, proactive IT integrates contract management with financial systems.
This ensures that spending aligns with donor rules and that reporting deadlines are met automatically. By linking vendors and payments back to specific grants, organizations can prove compliance during audits without scrambling through spreadsheets.
Choosing the Right Partner for Nonprofit IT Support
Selecting a technology partner is a strategic decision similar to hiring a key executive. Here are five criteria specific to the nonprofit sector:
- Experience with the nonprofit tech stack: Look for a provider who understands donor management systems like Raiser’s Edge or Salesforce NPSP. Also, they should grasp the specialized needs of donation processing and volunteer management.
- Transparent pricing with nonprofit discounts: Many providers offer discounts for 501(c)(3) organizations. Furthermore, you’ll want to avoid providers requiring large upfront hardware purchases when a monthly model would better suit your budget.
- Understanding of compliance details: The provider must demonstrate knowledge of PCI SAQ levels for donation pages and GDPR/CCPA requirements for international donors. If they don’t know what a tokenized payment gateway is, keep looking.
- A proactive mindset: Ask potential partners how they handle security. If they focus only on fixing broken computers, they are a break-fix shop. You need a partner who speaks about zero trust architecture, identity-first security, and quarterly security reviews.
- Scalability for Growth: Your IT needs during a capital campaign or disaster relief surge are different from your baseline operations. The right partner offers flexible contracts that scale up during high-volume fundraising seasons and scale down without penalty.

Hire IT Support for Nonprofits Today
The threats are real, from AI-driven scams and identity theft to supply chain vulnerabilities. By shifting the focus from the old concept of a network firewall to the new concept of identity and governance, organizations can protect their most sensitive asset: donor data.
Ready to lock down your donor data and unlock your fundraising potential? Contact SafePoint IT today. We specialize in translating complex security frameworks into practical and affordable IT support for nonprofits. Let’s build a strategy that protects your past, present, and future, so you can focus entirely on your mission.
Frequently Asked Questions
Why are nonprofits specifically targeted by cybercriminals?
Nonprofits are attractive targets because they hold valuable donor financial data and personally identifiable information. However, they often have fewer security resources than corporations, making them soft targets for ransomware and fraud.
Does accepting online donations make us automatically PCI compliant?
No, using a payment processor (like Stripe or PayPal) reduces your scope, but you are not automatically compliant. You must still complete a Self-Assessment Questionnaire annually, and ensure your website and IT infrastructure meet the security requirements outlined in the PCI DSS.
What is identity-first security, and why does it matter?
It is the principle that the user’s identity is the new security perimeter. Instead of just trusting the office network, you verify every login attempt and enforce phishing-resistant Multi-Factor Authentication.
You also need to monitor for suspicious behavior, ensuring that stolen passwords aren’t enough to cause a breach.
How does a managed IT provider handle after-hours emergencies?
A proactive provider operates a 24/7 Security Operations Center (SOC). If a server crashes at midnight or a ransomware attack begins on a Sunday, their team is alerted immediately. Then, work begins without waiting for your office to open on Monday.
Can we afford dedicated IT support on a limited budget?
Yes, outsourced IT support for nonprofits typically costs $100–$250 per user per month, which is often 30-50% less than hiring a full-time in-house IT generalist. Additionally, this model gives you access to a full team of specialists instead of relying on one person’s knowledge.

